Why Real-World Testing Matters
Controlled adversarial testing reveals what policy reviews and checklists never can
Expose Gaps Before Attackers Do
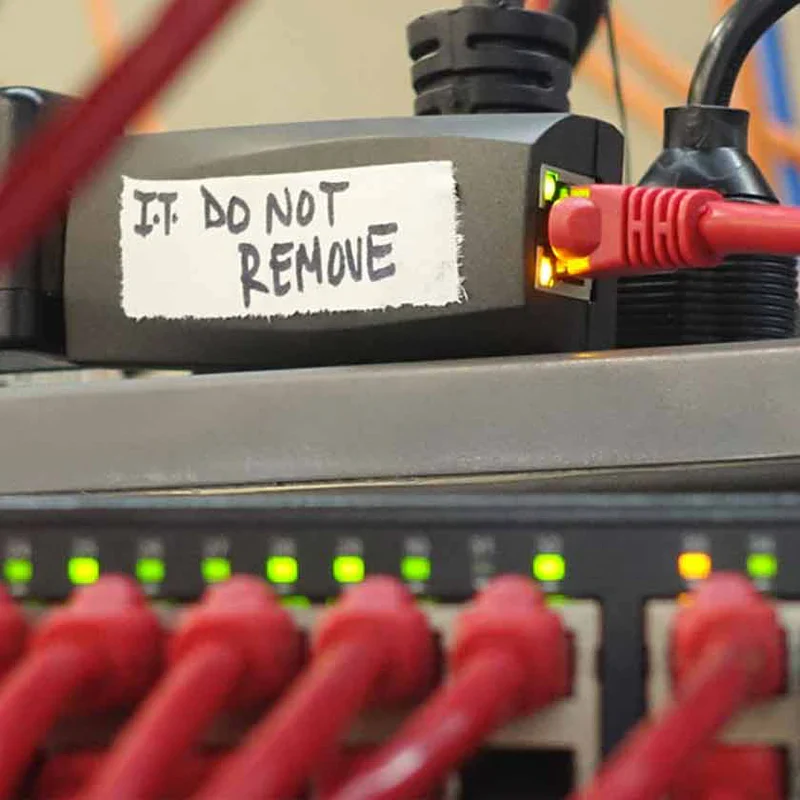
Documented policies and security training only go so far. The only reliable way to know how your people and physical controls hold up under pressure is to test them directly, under controlled, authorized conditions that mirror real attack scenarios.
Our penetration testing engagements focus exclusively on the human and physical attack surface: the vectors responsible for the vast majority of actual breaches. Every engagement is scoped and authorized in advance, with strict ethical safeguards throughout.
- Reveal which employees, departments, and entry points are highest-risk
- Validate whether existing security controls actually work in practice
- Test incident detection and response under realistic conditions
- Generate measurable data to track improvement over time
- Satisfy compliance requirements that mandate adversarial testing